04 Aug 2022
What is App Provisioning?
Let’s look at Azure Active Directory
In Azure Active Directory (Azure AD), the term app provisioning refers to automatically creating user identities and roles for applications.
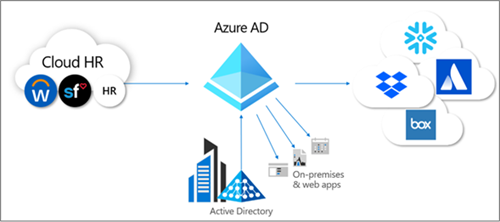
Azure AD application provisioning refers to automatically creating user identities and roles in the applications that users need access to. In addition to creating user identities, automatic provisioning includes the maintenance and removal of user identities as status or roles change. Common scenarios include provisioning an Azure AD user into SaaS applications like Dropbox, Salesforce, ServiceNow, and more.
Azure AD also supports provisioning users into applications hosted on-premises or in a virtual machine, without having to open up any firewalls. If your application supports SCIM, or you've built a SCIM gateway to connect to your legacy application, you can use the Azure AD Provisioning agent to directly connect with your application and automate provisioning and de-provisioning. If you have legacy applications that don't support SCIM and rely on an LDAP user store or a SQL database, Azure AD can support those as well.
App provisioning lets you:
- Automate provisioning: Automatically create new accounts in the right systems for new people when they join your team or organization.
- Automate de-provisioning: Automatically deactivate accounts in the right systems when people leave the team or organization.
- Synchronize data between systems: Ensure that the identities in your apps and systems are kept up to date based on changes in the directory or your human resources system.
- Provision groups: Provision groups to applications that support them.
- Govern access: Monitor and audit who has been provisioned into your applications.
- Seamlessly deploy in brownfield scenarios: Match existing identities between systems and allow for easy integration, even when users already exist in the target system.
- Use rich customization: Take advantage of customizable attribute mappings that define what user data should flow from the source system to the target system.
- Get alerts for critical events: The provisioning service provides alerts for critical events and allows for Log Analytics integration where you can define custom alerts to suit your business needs.
What is SCIM?
To help automate provisioning and deprovisioning, apps expose proprietary user and group APIs. But anyone who's tried to manage users in more than one app will tell you that every app tries to perform the same actions, such as creating or updating users, adding users to groups, or deprovisioning users. Yet, all these actions are implemented slightly differently by using different endpoint paths, different methods to specify user information, and a different schema to represent each element of information.
To address these challenges, the System for Cross-domain Identity Management (SCIM) specification provides a common user schema to help users move into, out of, and around apps. SCIM is becoming the de facto standard for provisioning and, when used with federation standards like Security Assertions Markup Language (SAML) or OpenID Connect (OIDC), provides administrators an end-to-end standards-based solution for access management.
For detailed guidance on developing a SCIM endpoint to automate the provisioning and de-provisioning of users and groups to an application, see Build a SCIM endpoint and configure user provisioning. For pre-integrated applications in the gallery, such as Slack, Azure Databricks, and Snowflake, you can skip the developer documentation and use the tutorials provided in Tutorials for integrating SaaS applications with Azure Active Directory.
Manual vs. automatic provisioning
Applications in the Azure AD gallery support one of two provisioning modes:
- Manualprovisioning means there's no automatic Azure AD provisioning connector for the app yet. User accounts must be created manually. Examples are adding users directly into the app's administrative portal or uploading a spreadsheet with user account detail. Consult the documentation provided by the app, or contact the app developer to determine what mechanisms are available.
- Automaticmeans that an Azure AD provisioning connector has been developed for this application. Follow the setup tutorial specific to setting up provisioning for the application. App tutorials can be found in Tutorials for integrating SaaS applications with Azure Active Directory.
The provisioning mode supported by an application is also visible on the Provisioning tab after you've added the application to your enterprise apps.
Benefits of automatic provisioning
As the number of applications used in modern organizations continues to grow, IT admins are tasked with access management at scale. Standards such as SAML or OIDC allow admins to quickly set up single sign-on (SSO), but access also requires users to be provisioned into the app. To many admins, provisioning means manually creating every user account or uploading CSV files each week. These processes are time-consuming, expensive, and error prone. Solutions such as SAML just-in-time (JIT) have been adopted to automate provisioning. Enterprises also need a solution to deprovision users when they leave the organization or no longer require access to certain apps based on role change.
Some common motivations for using automatic provisioning include:
- Maximizing the efficiency and accuracy of provisioning processes.
- Saving on costs associated with hosting and maintaining custom-developed provisioning solutions and scripts.
- Securing your organization by instantly removing users' identities from key SaaS apps when they leave the organization.
- Easily importing a large number of users into a particular SaaS application or system.
- Having a single set of policies to determine who is provisioned and who can sign into an app.
Azure AD user provisioning can help address these challenges. To learn more about how customers have been using Azure AD user provisioning, read the ASOS case study. The following video provides an overview of user provisioning in Azure AD.


